SSH was created because passwords got stolen lol
Just a guy who loves to write code and watch anime.
Introduction
Before Secure Shell (SSH) existed, the internet wasn't very safe. People used things like Telnet and rlogin to access systems remotely, but these sent data without any protection. This made it easy for bad people to steal important information, which was a big security problem. There was a need for a safer way to access systems remotely, but nobody had found a solution yet.
The Birth of SSH
The SSH story starts with a Finnish researcher named Tatu Ylönen. In 1995, after someone stole passwords from his university network, he wanted to make a safer way to access systems remotely. He created SSH, a method that let people use network services safely, even on unsafe networks. SSH was a big improvement for internet security, fixing not only password stealing but also other major cybersecurity problems.
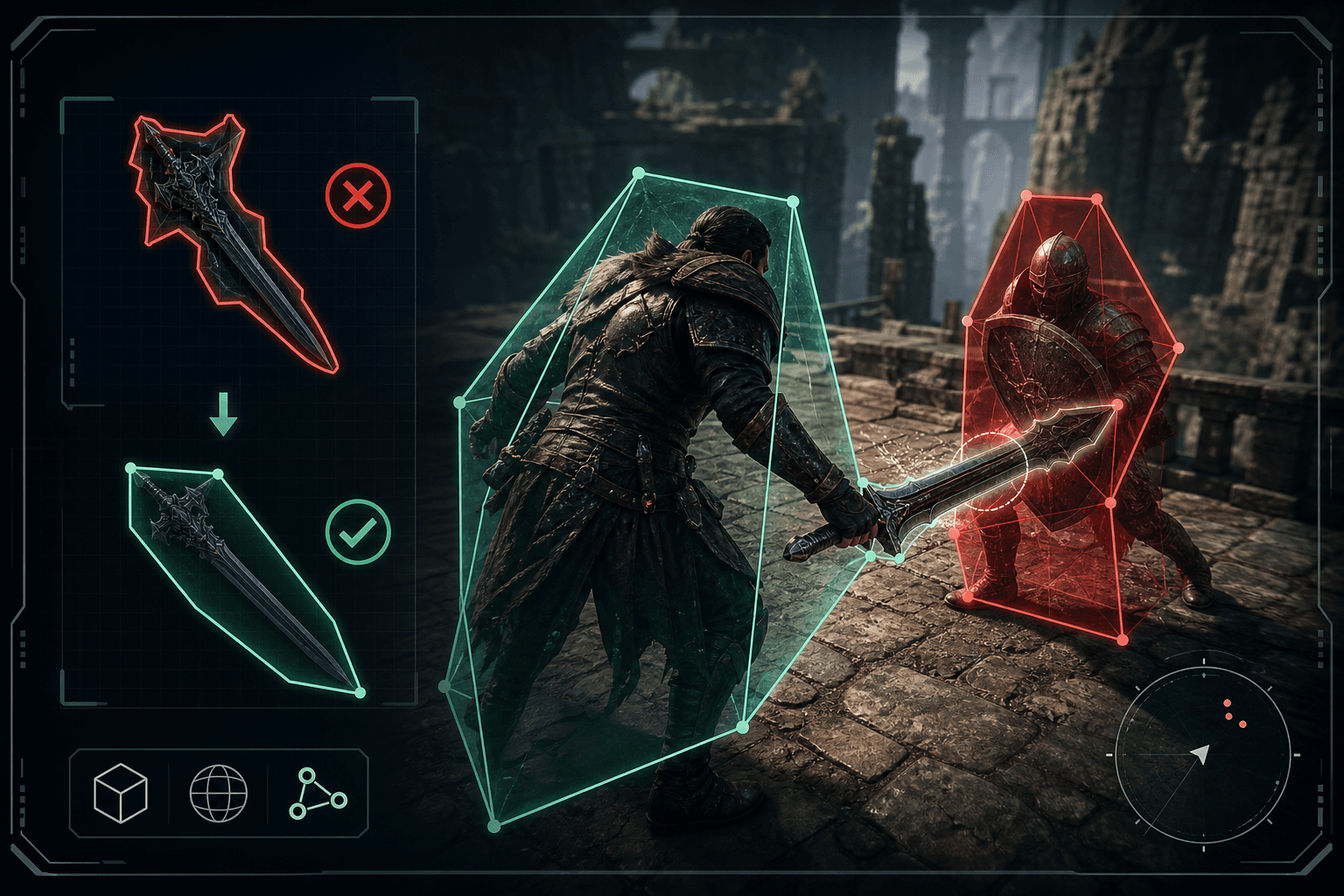
How SSH Works
SSH uses a client-server model to help two remote systems authenticate and encrypt the data they share. It provides users with cryptographic keys, which act like usernames and passwords.
System administrators often use these keys to access systems. By default, SSH works on TCP port 22, but this can be changed if necessary. The host (server) listens on this port for incoming connections and sets up a secure connection by verifying the client and opening the right shell.
SSH Flow
Key Generation and Saving: The SSH client generates a pair of cryptographic keys, a public key and a private key. The public key is saved to the SSH server to establish a trust relationship.
Login Request: The client starts a session with the SSH server by sending a login request.
Encrypted Challenge: The server sends an encrypted random number to the client. This is done to ensure that the client is in possession of the corresponding private key and can decrypt this challenge.
Decryption and Response: The client uses its private key to decrypt the random number and sends the decrypted information back to the server.
Verification: Upon receiving the decrypted information, the server uses the previously saved public key to verify that the information is correct, confirming the client's identity.

Understanding SSH Packets
SSH packets are the basic pieces of data sent in the SSH protocol.
Each packet is structured in a specific format, as defined by RFC 4253.
The packet consists of several components:
Packet Length: This is the length of the packet in bytes, excluding the HMAC value or the Packet Length field itself.
Padding Length: This represents the length of the Random Padding in bytes.
Payload: This is the useful contents of the packet.
Random Padding: This is random-length padding that makes the total packet size (including packet_length, padding_length, payload, and random padding) a multiple of the cipher block size or 8, whichever is bigger. There must be at least four bytes of padding. The padding should be made of random bytes, and the most padding allowed is 255 bytes.
MAC (Message Authentication Code): This field contains the MAC value. If message authentication has been negotiated, this field contains the MAC bytes.
Multiple Channels in SSH
SSH lets you create multiple channels within one SSH session. This feature allows for many operations to happen over a single SSH connection. Each channel handles one service. For example, you could run a process, download a file using SFTP, and forward multiple ports all at once with one SSH connection.
In reality, these operations don't happen at the same time but share the connection's bandwidth in a "time-share" way. This makes working with SSH more challenging than other protocols like HTTP or Telnet.
Multiplexing, or sending more than one signal over a single line or connection, is a feature of OpenSSH. This allows reusing an existing outgoing TCP connection, which avoids the need for a new TCP connection for each SSH session.
The Evolution of SSH
SSH has evolved over time, with the introduction of SSH-2 in 1996 to address problems and limitations discovered in the original SSH-1 protocol. Today, there are dozens of SSH implementations, both free and commercial, for virtually all platforms, and it is used by millions of people worldwide to secure their communications.
Who Uses SSH and Why
SSH is used in many different situations. Almost every data center in the world uses it, and it's found in more than half of the world's websites.
People use it to handle networks, transfer files securely and automate tasks between machines.
Some typical uses for SSH include safely accessing resources remotely, running commands from a distance, providing software fixes and updates, and transferring files both manually and automatically. SSH keys are often used in scripts, backup systems, and tools for managing configurations.
SSH for Developers
As a developer, you might use SSH for a variety of tasks.
For example, you might use it to securely log in to a remote server for a terminal emulation session.
A common example is connecting with Github via SSH.
Conclusion
In conclusion, SSH has revolutionized the way we secure internet communications. Big shout out to the man himself, Tatu Ylönen. Thanks for SSH.